Introduction
In today’s data-driven enterprise landscape, organizations require secure, high-performance database solutions that can handle both transactional and analytical workloads while maintaining security and compliance requirements. SAP HANA Cloud on AWS, a cornerstone of SAP Business Technology Platform (SAP BTP), addresses these needs as a fully managed, cloud-native database-as-a-service offering.
Common use cases for SAP HANA Cloud include running core business applications such as ERP, CRM, HR, and logistics on a single, high-speed platform, as well as supporting advanced analytics and intelligent data applications that drive actionable insights and business innovation. SAP HANA Cloud is also the foundation of SAP BTP services such as SAP Analytics Cloud, SAP Datasphere and self-developed applications built with SAP Cloud Application Programming Model (CAP).
This blog post focuses on enhancing SAP HANA Cloud’s security and connectivity through AWS PrivateLink, addressing a critical need for organizations requiring private, secure database access while maintaining high performance and reliability.
Why SAP HANA Cloud on AWS?
SAP HANA Cloud is powered by AWS Graviton processors, delivering up to 30% better compute performance for analytical workloads, lowering compute costs by 15%, and using up to 60% less energy compared to comparable EC2 instances. By migrating to AWS Graviton-based instances, SAP can reduce the compute carbon footprint of SAP HANA Cloud workloads by an estimated 45%, supporting their commitment as a signatory of Amazon’s The Climate Pledge to help reduce carbon emissions. SAP plans to expand its use of AWS Graviton in the future to continue leveraging these performance gains, cost savings, and energy efficiencies. Hence customers using SAP HANA Cloud on AWS would benefit from the performance improvement and reduced carbon footprint.
Connecting to SAP HANA Cloud on AWS
When connecting to SAP HANA Cloud, client applications or users, whether on-premises or in other cloud environments, can securely access the database using public APIs through an internet-accessible endpoint.
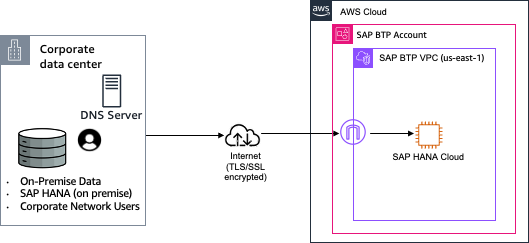 Figure 1: Connecting to SAP HANA Cloud via the default public endpoint
Figure 1: Connecting to SAP HANA Cloud via the default public endpoint
However, customers in regulated industries such as financial services, healthcare and government agencies, with regulations such as HIPAA, EU/US Privacy Shield, and PCI DSS, may have security requirements where public endpoints cannot be used. In this case, we recommend combining SAP HANA Cloud with AWS PrivateLink which enables secure and private communication between your databases and applications while leveraging AWS’s secure network infrastructure. By using private IP address ranges (RFC 1918), you reduce the attack surface of the service.
This blog post explains how you can enhance data-in-transit security for SAP HANA Cloud by leveraging the private connectivity option with AWS PrivateLink. PrivateLink enables secure, private network connections between your AWS environment and SAP HANA Cloud, eliminating exposure to the public internet and reducing the risk of unauthorized access.
What is AWS PrivateLink?
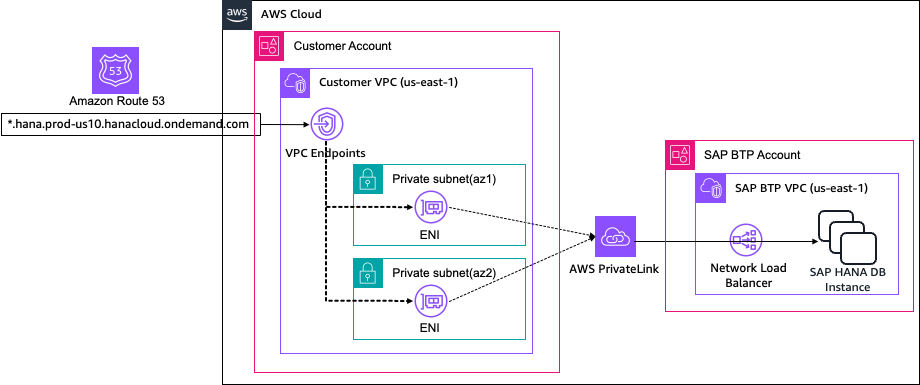
AWS PrivateLink provides private connectivity between your AWS services (networks, compute, serverless applications, AI etc.) and SAP BTP services – without exposing the traffic to the public internet. You can also use AWS PrivateLink to provide a secure and private connection between your on-premises networks connected through Direct Connect or VPN to your Amazon Virtual Private Cloud (VPC) – avoiding public networks or IPs entirely.
AWS PrivateLink makes it easy to connect services across different accounts and VPCs to significantly simplify your network architecture. It enables you to connect to AWS services, services hosted by other AWS accounts (referred to as endpoint services), and to AWS Marketplace partner services, via interface endpoints, that are elastic network interfaces with private IP addresses in your VPC.
Interface endpoints are created directly inside of your VPC, using elastic network interfaces and IP addresses in your VPC’s subnets. Providers and consumers do not have to align network segments or CIDR blocks to avoid overlapping IP ranges. VPC Peering or connection via AWS Transit Gateway is not needed for the communication. You can associate security groups and attach an endpoint policy to interface endpoints of AWS services, to control access to a specified service. With AWS PrivateLink, you can access AWS services or other services, provided by another VPC, securely through private connectivity within the AWS network. All network traffic stays on the global AWS backbone and is not traversing the public internet.
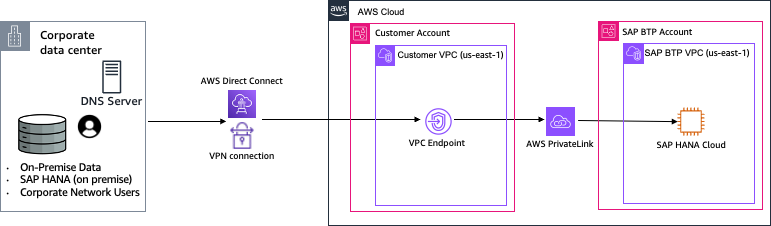 Figure 2: Connecting to SAP HANA Cloud via AWS PrivateLink
Figure 2: Connecting to SAP HANA Cloud via AWS PrivateLink
To better understand the advantages of AWS PrivateLink integration with HANA Cloud, let’s explore several practical use cases that demonstrate its benefits in real-world scenarios.
SAP HANA Cloud and AWS PrivateLink – Example Use Cases
In a business landscape where data security is critical, implementing AWS PrivateLink is essential for protecting sensitive information during data transfers. The private IP endpoint service, provided by AWS’s infrastructure, acts as a crucial security layer that helps prevent potential security breaches that could otherwise result in significant business impact. This integration demonstrates AWS’s commitment to providing enterprise-grade security solutions that address the complex requirements of modern cloud architectures.
Use Case 1 – SAP HANA Cloud Administrative Access Security
One of the most compelling use cases for implementing SAP HANA Cloud PrivateLink addresses the critical need for secure database access. In a typical enterprise environment, database administrators and developers working from corporate offices require regular access to SAP HANA Cloud to perform essential table management, maintenance, and development tasks. These technical professionals, unlike regular users, are granted extensive database privileges necessary for their roles, making their connection security particularly crucial.
Figure 3 shows SAP HANA Cloud with AWS PrivateLink provides the perfect solution by enabling organizations to restrict the transfer of sensitive organizational data to private networks only. Private network access to database operations eliminates public IP exposure while maintaining operational efficiency, strengthening an organization’s security posture through strict access controls.
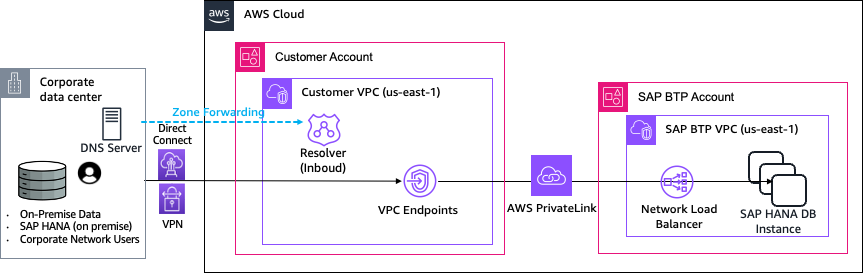 Figure 3: SAP HANA Cloud Administrative Access Security
Figure 3: SAP HANA Cloud Administrative Access Security
Use Case 2 – Secure Data Platform Integration: SAP HANA Cloud and AWS Services
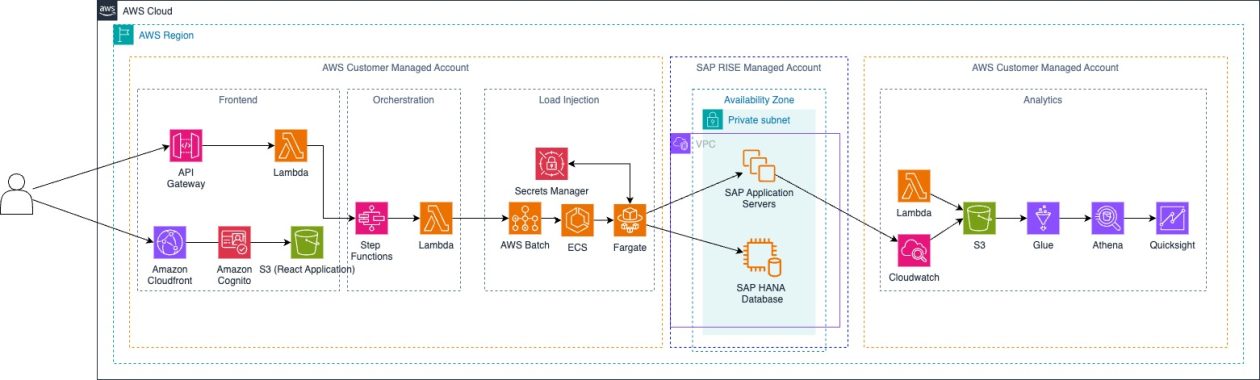
A significant use case for SAP HANA Cloud and AWS PrivateLink emerges when you build your data platforms on AWS and need to integrate SAP HANA Cloud data into your analytics ecosystem. There are two primary methods for accessing SAP HANA Cloud data within AWS data platforms: using AWS Glue ETL jobs to extract and load data into Amazon S3, or employing Amazon Athena SAP HANA Connector for federated queries. Both approaches require secure and reliable connectivity between AWS services and SAP HANA Cloud.
When implementing these data integration patterns, security becomes paramount as sensitive business data moves between systems. Figure 4 shows AWS PrivateLink provides the necessary secure connectivity layer, ensuring that all data transfers and queries between AWS services (such as AWS Glue and Amazon Athena) and SAP HANA Cloud occur through private network channels, eliminating exposure to the public internet and meeting stringent security requirements for enterprise data integration scenarios.
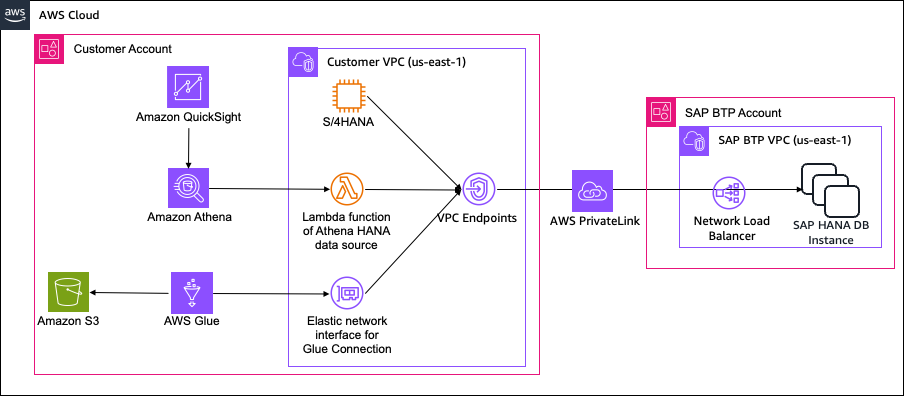 Figure 4: Secure Data Platform Integration : SAP HANA Cloud and AWS Services
Figure 4: Secure Data Platform Integration : SAP HANA Cloud and AWS Services
How to setup SAP HANA Cloud with AWS PrivateLink
Let’s walk through the setup of use case 1 an enterprise-grade SAP HANA Cloud access. This blog referred to SAP HANA Cloud Administration Guide for the configuration. This configuration is available in SAP BTP paid tier account. At the time of writing this blog, SAP HANA Cloud PrivateLink for data lake instances is only available for AWS, and only supports connections within a region as described in SAP HANA Cloud PrivateLink document. Following are the configuration steps overview.
- Enable the AWS PrivateLink Endpoint ID within SAP HANA Cloud
- Configure VPC Endpoint in AWS VPC
- Add AWS VPC Endpoint to HANA Cloud instance allow list
- Configure Private Hosted Zone in Amazon Route53
- Test the private routing from inside VPC to HANA Cloud
- Configure Resolver for Inbound DNS query forwarding (Only Required for Use case 1 with RISE or On-premise network)
Following is the details for each steps. For further steps by steps guidance please refer to lab in this workshop
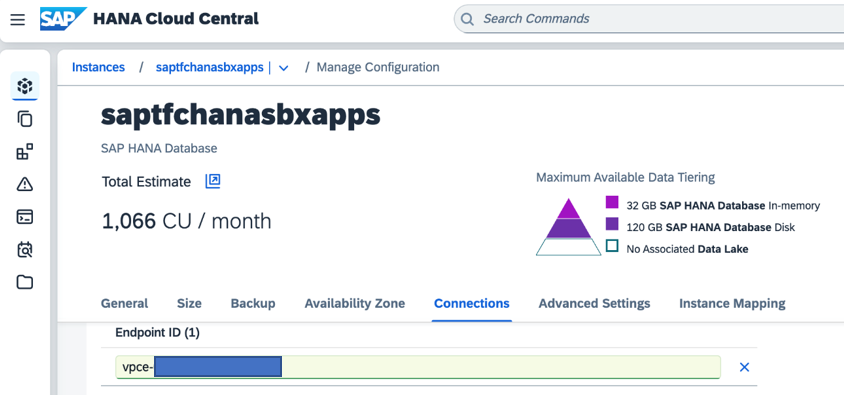
1. Enable the AWS PrivateLink Endpoint ID within SAP HANA Cloud
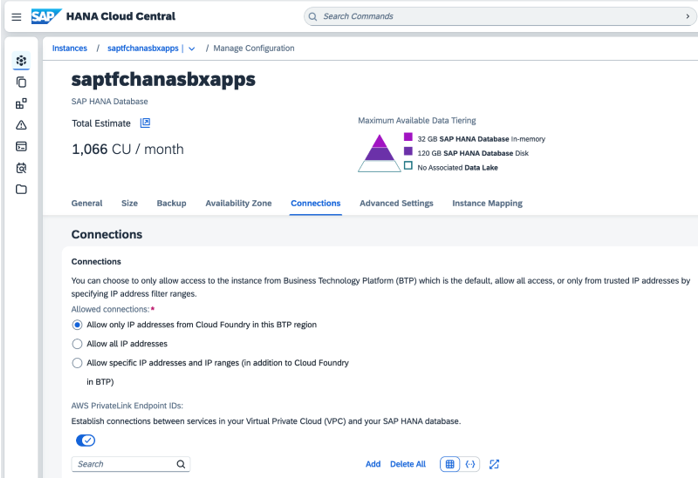
In the SAP HANA Cloud central screen, choose the HANA Cloud instance you want to configure and click View Configuration.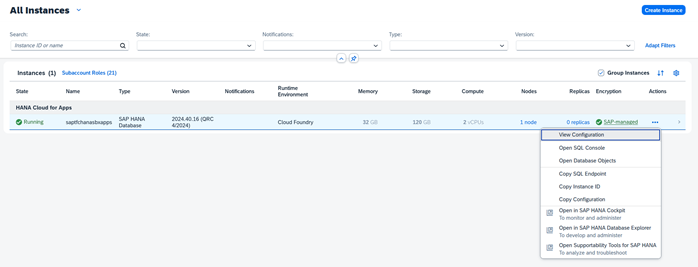
Figure 5: SAP HANA Cloud – View Configuration
In the Connections tab, turn ON the button to enable AWS PrivateLink Endpoint IDs. This will enable you to obtain the PrivateLink Endpoint IDs to setup connection your own AWS VPC. In Allowed connections, choose “Allow only IP addresses from Cloud Foundry in this BTP region” or “Allow specific IP addresses and IP ranges (in addition to Cloud Foundry in BTP)” to make sure all traffic will go through private connection.
Figure 6: SAP HANA Cloud – Connections
2. Configure VPC Endpoint in AWS VPC
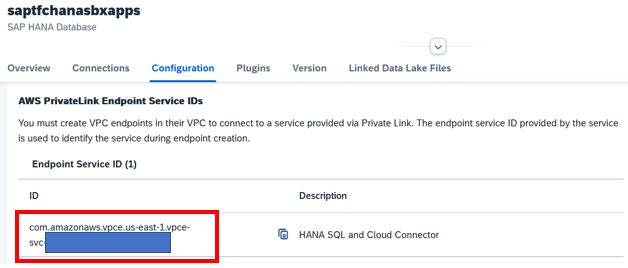
In this step, we will configure a VPC Endpoint in AWS VPC and a security group to allow access from Amazon VPC to HANA Cloud via this endpoint. If you don’t have any VPC setup in your own AWS account, please refer Amazon VPC document to create a VPC. Copy AWS PrivateLink Endpoint Service IDs in the Configuration tab of SAP HANA Cloud instance.
Figure 7: SAP HANA Cloud – PrivateLink Endpoint Service IDs
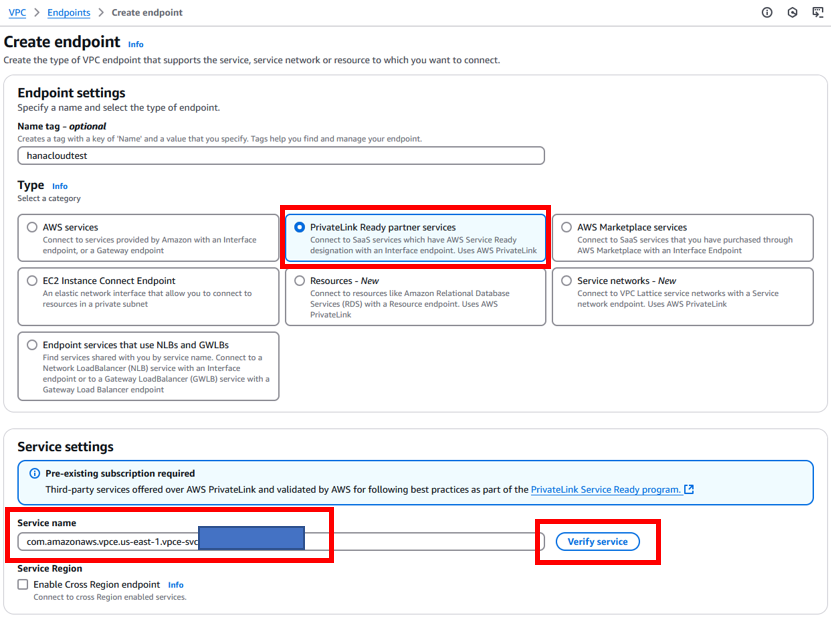
In AWS Console, access Amazon VPC service and create an VPC Interface Endpoint for partner services. In Endpoint creation screen, enter Name for the endpoint, choose “PrivateLink Ready partner services” for Type. In Service settings, input the AWS PrivateLink Endpoint Service IDs of HANA Cloud instance to Service name box. Then click Verify service button.
Figure 8: Amazon VPC – Create VPC Endpoint(1)
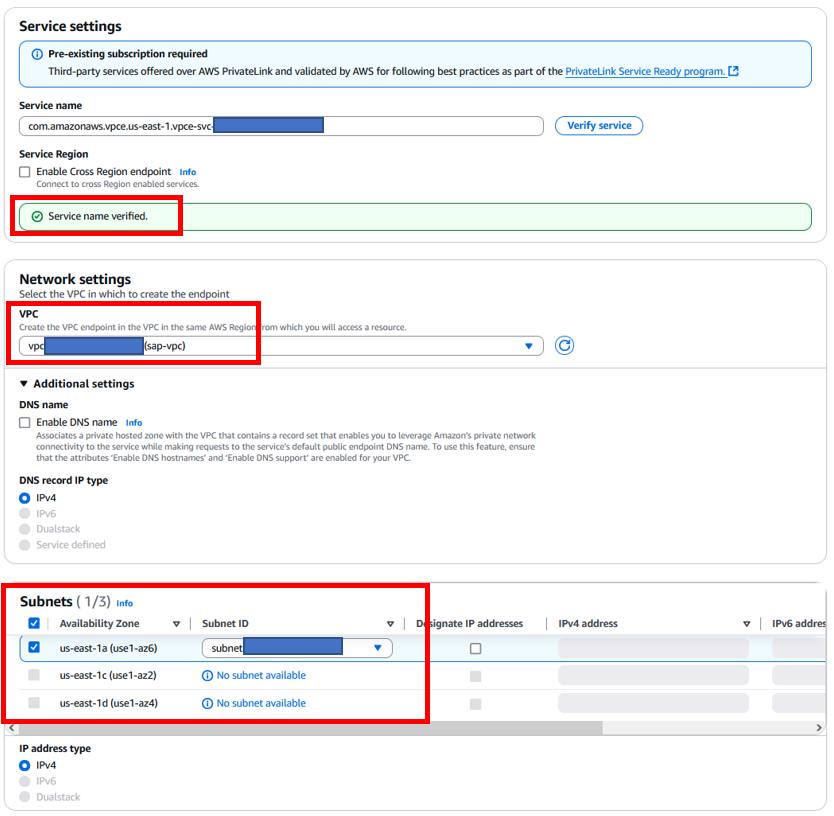
When the successful message “Service name verified” displayed, you will be able to select the Network settings. In Network settings, select the VPC and Availability Zone, Subnet to setup the endpoint. If your SAP HANA Cloud instance is multiple AZs available, you will be able to select multiple AZs and Subnets in your VPC.
Figure 9: Amazon VPC – Create VPC Endpoint(2)
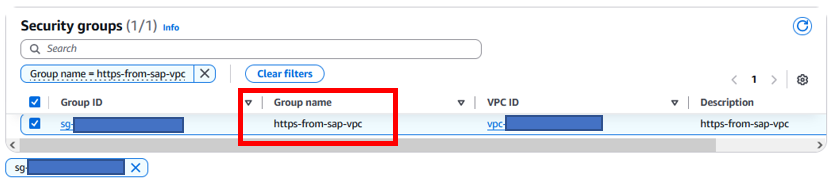
Please assign the security group which allows inbound https traffic for this endpoint. In this blog, we created a security group name https-from-sap-vpc which has inbound rules to allow https traffic from VPC IP address CIDR.
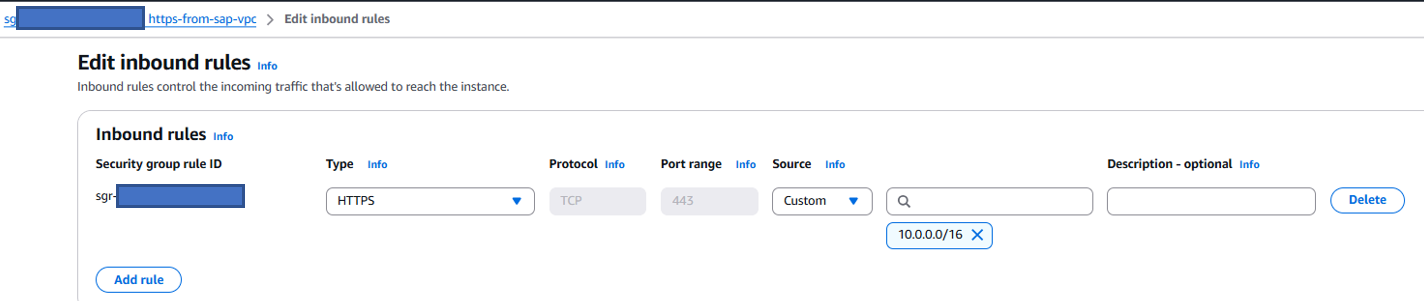 Figure 10: Amazon VPC – Create VPC Endpoint(3)
Figure 10: Amazon VPC – Create VPC Endpoint(3)
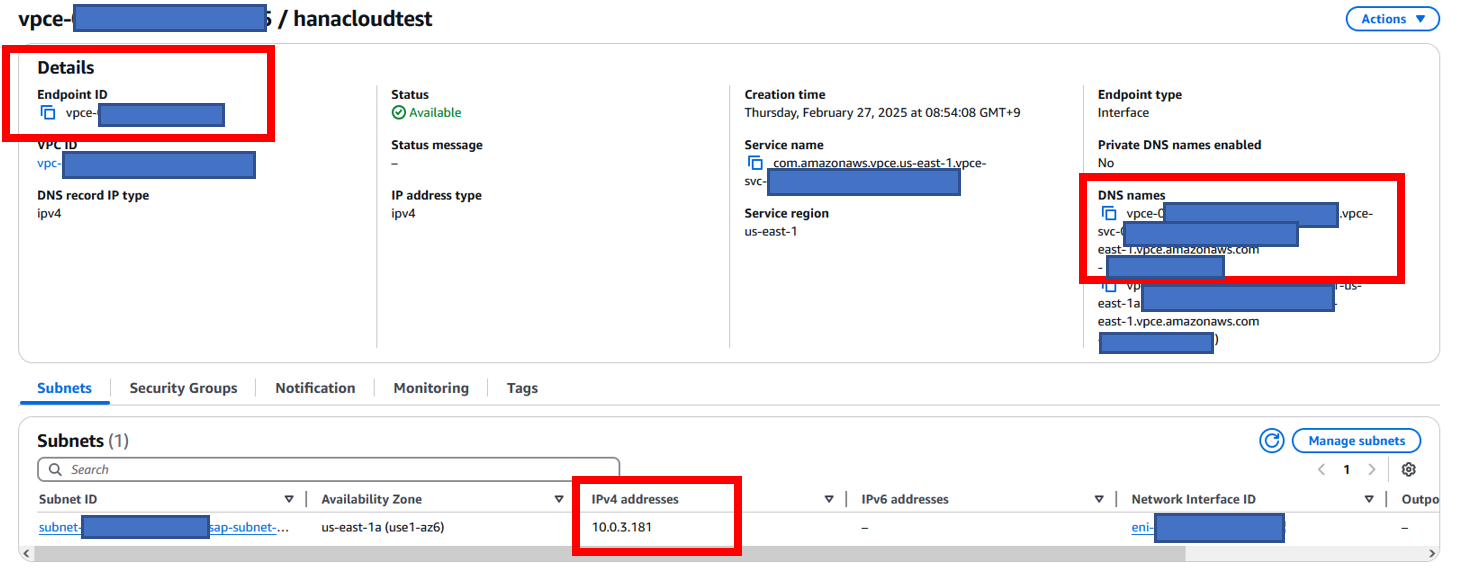
After the VPC Endpoint is created, and has the status available, copy the Endpoint ID in the endpoint details page. This ID will be used to input to HANA Cloud configuration in the next step. Copy the DNS name to be used in later DNS configuration in Route 53. Note down the private IPv4 address, you can confirm this in the last step when we test the private routing.
Figure 11: Amazon VPC – Display VPC Endpoint
3. Add Amazon VPC Endpoint to HANA Cloud instance allow list
Go back to the HANA Cloud Central screen, and open your HANA Cloud instance configuration. In Connection configuration, add the created VPC endpoint ID to the allow list. This will allow the created VPC endpoint from your VPC to connect to HANA Cloud PrivateLink Endpoint service.
Figure 12: SAP HANA Cloud – Allow VPC Endpoint ID
4. Configure Private Hosted Zone in Amazon Route53
This step is to set up a private hosted zone of Amazon Route 53 for your VPC, then create the DNS record to direct the traffic to the HANA Cloud instance to the VPC Endpoint.
From SAP HANA Cloud Connections details, you can see the SQL endpoint address and landscape address. Please note down these address to use in Route 53 DNS setting and connection testing.
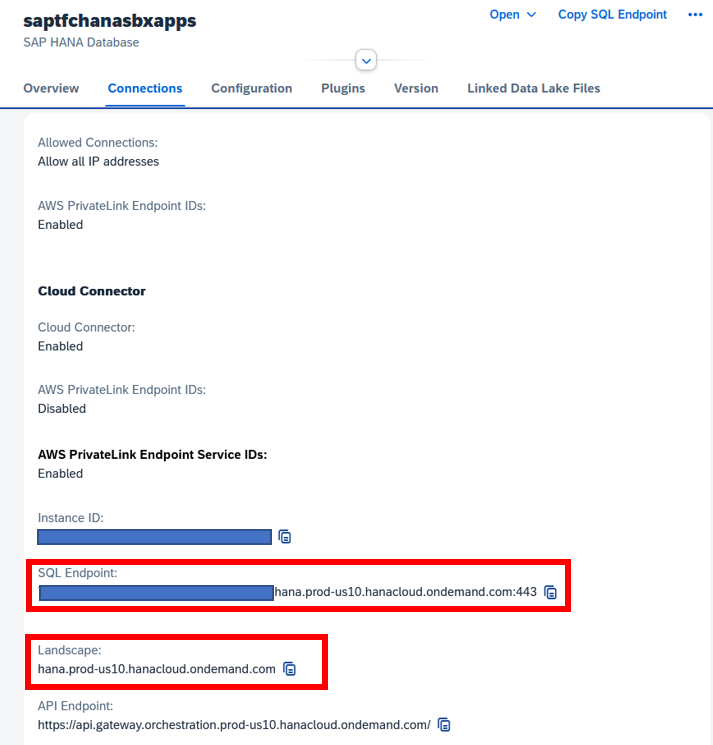 Figure 13: SAP HANA Cloud – Display Connection
Figure 13: SAP HANA Cloud – Display Connection
In Amazon Route 53 Hosted zone configuration, set the value as following:
– Put the HANA Cloud landscape name as Domain name
– Select Private hosted zone as type
– Select your VPC ID to associate the hosted zones with your VPC
Then click on the Create hosted zone button.
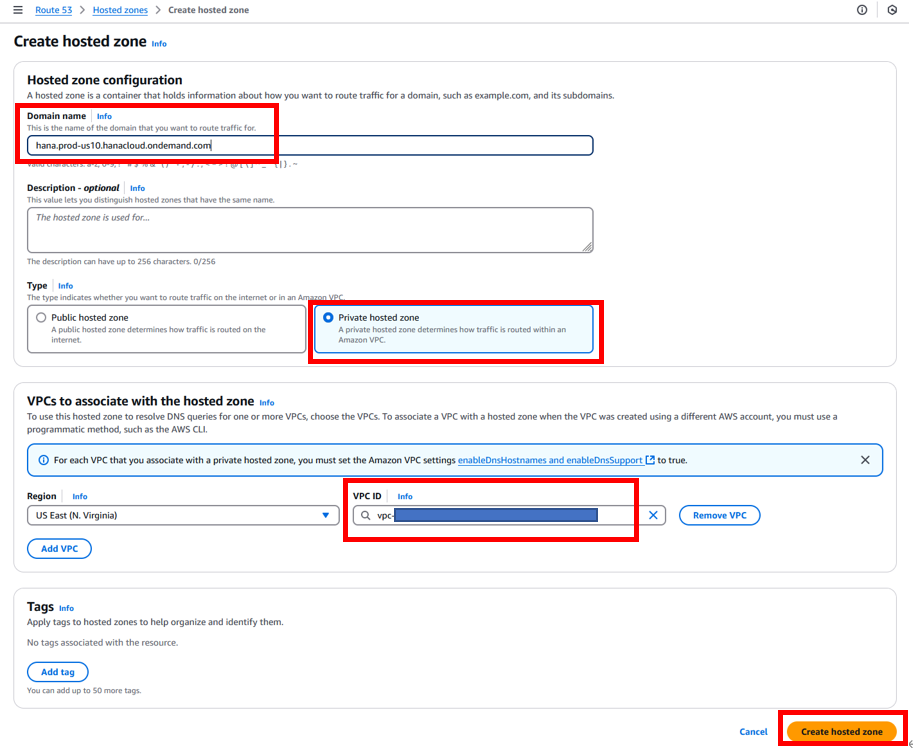 Figure 14: Amazon Route 53 – Create hosted zone
Figure 14: Amazon Route 53 – Create hosted zone
In the created hosted zone screen, create a new DNS record to route all HANA Cloud traffic to the VPC Endpoint.
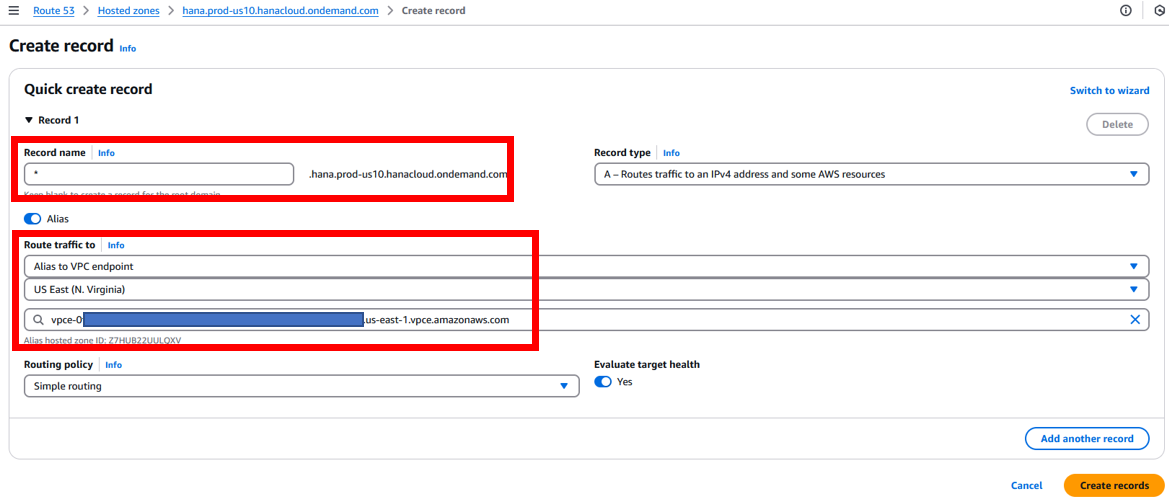 Figure 15: Amazon Route 53 – Create record
Figure 15: Amazon Route 53 – Create record
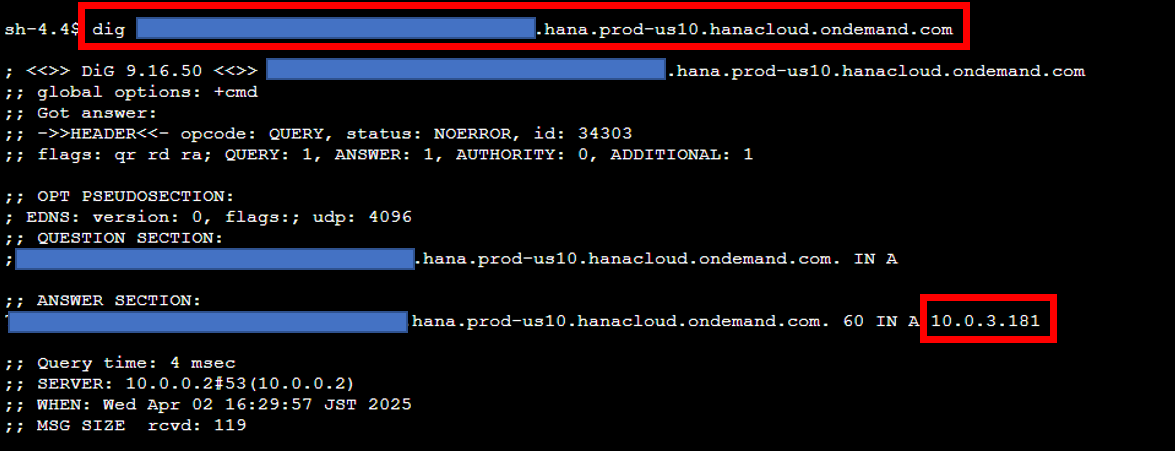
5. Test the private routing from inside VPC to HANA Cloud
After finishing the configuration, check that the traffic to HANA Cloud instance is going to the private IP address of the VPC endpoint, by executing dig or nslookup command from an EC2 instance inside VPC. Executing these commands with the HANA Cloud endpoint URL, will answer with the private IP address of the VPC Endpoint.
Figure 16: Verified the private routing by dig command
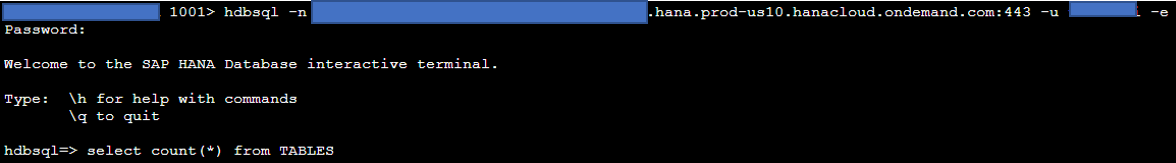
verify the database connection by hdbsql command to HANA Cloud endpoint.
Figure 17: Verified the database connection by hdbsql command
6. Configure Resolver for Inbound DNS query forwarding (Only Required for Usecase 1 with RISE or On-premise network)
Since the Route 53 private hosted zone is setup inside your AWS Account’s VPC, it only impact the traffic from instance in this VPC. In Use case 1, when you want the traffic from RISE or On-premise network to HANA Cloud also able to go through VPC endpoint, you need to use Route 53 Inbound Resolver, and forward the DNS from your network to this resolver.
The details instruction can be referred in Route 53 document. The screen bellow is a sample of Inbound endpoint created within VPC and it has 2 private IP addresses assigned in 2 subnets. We can use these IP address for DNS setting in RISE or On-premise network.
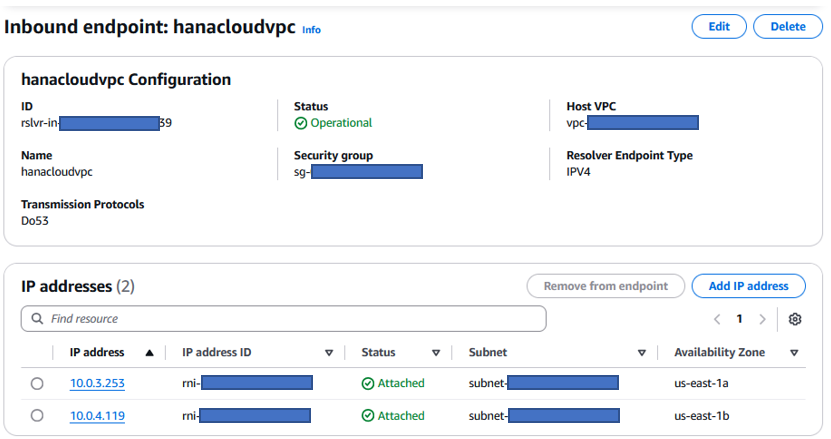 Figure 18: Amazon Route 53 – Inbound Resolver
Figure 18: Amazon Route 53 – Inbound Resolver
High Availability
AWS PrivateLink’s high availability architecture provides you with robust and resilient connectivity through multiple Availability Zones (AZs), ensuring continuous service availability for critical business operations. Figure 19 shows by implementing AWS PrivateLink with multiple endpoint network interfaces across different AZs, you can achieve automatic failover capabilities and eliminate single points of failure in their network architecture. This distributed design allows traffic to automatically route to healthy endpoints if an AZ becomes unavailable, maintaining seamless connectivity for applications and services. You benefit from improved application reliability, reduced downtime risks, and consistent performance while maintaining the security advantages of private connectivity. Additionally, AWS PrivateLink’s integration with Amazon Route 53 DNS service enables intelligent routing and health checking, further enhancing the overall availability and fault tolerance of the solution. This comprehensive high availability implementation helps you to meet your stringent business continuity requirements while maintaining secure and private network communications.
The following architecture explains how HA works across 2 AZs though Network Load Balancer.
Figure 19: AWS PrivateLink with High Availablity
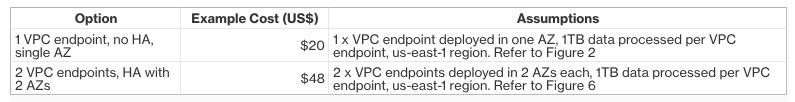
Pricing Examples
At the time of publishing this blog, there are no additional charges within SAP BTP when enabling AWS PrivateLink for SAP HANA Cloud. SAP is responsible of the implementation and activation of the Network Load Balancer. You are only charged for the resources, created in your own AWS account.
For example, let’s compare the costs of AWS PrivateLink in the customer’s AWS account with and without High Availability. Both options are in this AWS Pricing calculator link:
Figure 20: Pricing Examples
What’s next?
To find out more about AWS PrivateLink, refer to the AWS documentation “What is AWS PrivateLink?”, “Connect your VPC to services using AWS PrivateLink and the AWS whitepaper “AWS PrivateLink”.
Likewise, refer to the SAP HANA Cloud online documentation and SAP HANA Cloud Database Administration Guide for further details.
In addition to your AWS account team and AWS Support channels, we launched re:Post – A Reimagined Q&A Experience for the AWS Community. Our AWS for SAP Solution Architecture team regularly monitor the AWS for SAP topic for discussion and questions that could be answered to assist our customers and partners. If your question is not support-related, consider joining the discussion over at re:Post and adding to the community knowledge base.
Credits
We would like to thank Derek Ewell, Ferry Mulyadi, Diego Lombardini and Eneko Bilbao for their contributions to this blog.











 English (US) ·
English (US) ·